So what is “Blockchain”?
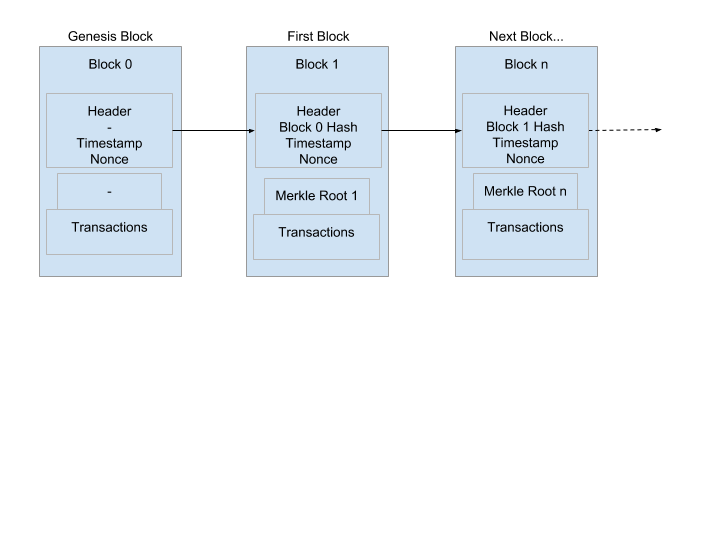
As the name suggests Blockchain has blocks connected by a chain. A chain of blocks containing digital information. Each block has a code called a hash. A hash is a set of characters (eg. “1hi715A719H” ) made up of the information contained in the block.
The next block contains the previous block’s hash and that joins them permanently together in an unchangeable sequence.
As the first Block in the chain cannot contain the hash of a previous block, this is called the genesis block. Here is a simplified diagram of a blockchain.
Security
If someone tried to change one of the blocks the next block would not contain the correct hash so the chain would break.
Even if someone were successful in maliciously updating all the subsequent blocks, as there is no single copy where the data is stored all the nodes in the chain wouldn’t be the same. A copy of the program and the data is stored on every computer in the chain and updated by executing all the programs. Therefore if erroneous changes occur the majority would overrule and disregard the malicious changes. But of course only 51% is enough to be a majority, so if 51% of the nodes were compromised, the information they hold would be considered true. This was a known flaw at the inception of blockchain and is so called the “51% Attack”.
So like everything in life, Blockchain is not 100% safe. With no central server to store the data if every computer in the chain were to go down the chain would be dead.
A blockchain banking system
One critical thing that a payment network need to ensure does not happen is spending the same amount twice or “double-spending”, as it is known. Traditionally, a trusted third party controlling a central server to keep records of transactions and balances was the only solution.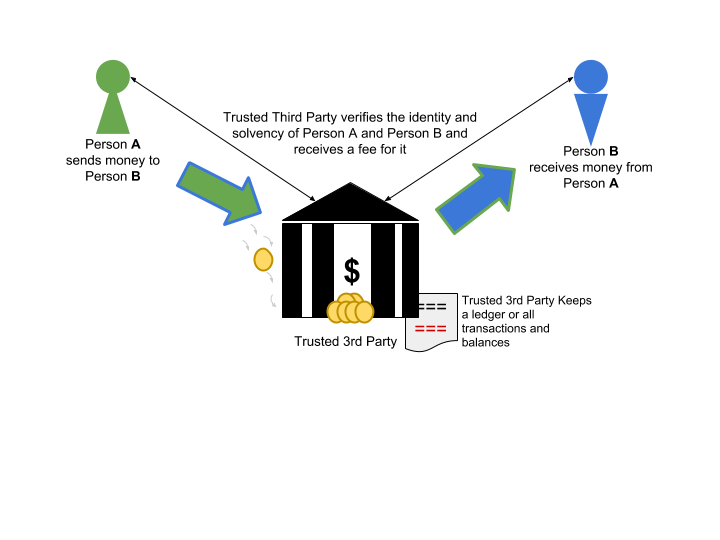
An authority in control of the funds and personal details of the users is required for this to work, and this is what we see in traditional banking systems closely controlled by governments and banks, who make considerable profits from being the ‘middleman’ in this arrangement.
Blockchain offers a fresh alternative to the traditional banking model with no Trusted 3rd Party blockchain relies on consensus to verify transactions.
Blockchain and Energy consumption
Opponents of Blockchain or more specifically cryptocurrencies, are quick to point out one major downside of blockchain, it is energy inefficient. As they are distributed systems that constantly re-record data on every node, this is data which they have already have, but to ensure consensus and security, each time a transaction in the ledger is created every node has to rewrite their copy of the distributed ledger. This means the bigger they grow the more energy they consume. And mining exponentially consumes more and more power as more miners join, the more complex the ‘puzzles’ become, the more energy is required to make the growing number of hashes.
Download An essential Guide to blockchain eBook
An essential Guide to Blockchain
What are Nodes?
A node is a powerful computer that runs the cryptocurrency software and keeps the blockchain alive. Running a node is as simple as downloading free software and configuring a normal computer, with enough storage space and processing power, and setting its connection to leave a certain port open. Running a node consumes a lot of energy and storage space. One of the biggest costs to mining is the electricity running costs and the high end processor. Graphics cards have been proved as best suited processors for mining. And some of the top hardware vendors such as NVIDIA are launching graphics cards specifically geared towards the task of mining crypto.
Watch this video explanation about nodes
Nodes send information about cryptocurrency transactions across the network by sending to other nodes that it is aware of. A node doesn’t need to know all the nodes in the chain. But each node that a node is aware of is aware of different nodes and so the network grows and the information goes across the entire network quick quickly.
Not all nodes are involved in the task of mining some just spread the information.
The Mining nodes run the task of grouping outstanding transactions into blocks and adding them to the blockchain by solving a complex mathematical puzzle in the cryptocurrency software. The puzzle is to find a number that is the result of combining the data in the block and passing it through what is called a hash function. This produces an integer (number) which is called a nonce. Each cryptocurrency will have a range that all the nonces will be between. For example the range for Bitcoin is 0 and 4,294,967,296.
The hash function disguises the number and makes it impossible to predict the output so a miner actually has to guess the number and apply the hash function to a combination of that number and the data in the block.
It is impossible to know which number will work. Two consecutive integers produce very different results and there may be more than one nonce that produces the result, or none.
When a miner gets a hash result within the target range the success is announced to the whole network and the miner gets rewarded some new crypto coins for the success. Other miners in the network stop working on that block and start searching for the number for the next block.
What is mining?
We know that digital or cryptocurrencies are not something we can touch so we can easily guess that mining is not the same physical process as mining for coal or mining for precious metals. But many people don’t understand the process or even why do we call it mining?
Cryptocurrency exists but needs discovering, we don’t know exactly where it is. So in that way it is similar to mining. Cryptocurrencies exist in their protocol’s design (like gold or diamonds exist underground), but they haven’t been discovered or revealed yet (again like gold or Diamonds).
We know that the Bitcoin protocol is coded so that a total of 21 million bitcoins will exist at some point. What “miners” do is discover or reveal them, a few at a time. Cryptocoin designers do not need to limit the number, but there are many reasons why they might choose to.
Miners are give a known partial input and they must guess the hashed output which is derived from the current state of the blockchain. It is completely random so there is no way to mathematically predict the output. The miners need to guess by trying many different combinations containing the known ’partial’ input and the required number of zeros at the end. As you can imagine, this requires many attempts to correctly guess so computers are used to generated and try many variations until the correct one is discovered.
New cryptocurrencies are revealed as a reward for the creating validated transaction blocks and adding them into the blockchain. It is this incentive that miners receive that ensures that they all agree on the ledger being correct.
Before any transaction on the network is processed it must be validated, to be validated miners must ‘guess’ the key. The key allows the transaction to be added to the open ledger. Guessing the key enables the miner who guessed it first to re-publish the ledger with the new transaction added and receive a financial reward (usually paid in the cryptocurrency of the blockchain). The other miners can no longer earn a reward from that transaction, so they want to start work on the next transaction. In order to do that they need to accept the new ledger and they add it to their own distributed copy.
The more miners that join the network, the more complicated the hash becomes. This is to balance the number of blocks that can be found. On average one block every 10 mins is allowed.
The Mining Rig
A Mining rig is the computer used to mine cryptocurrency. A rig can be dedicated for that purpose or a computer used for other tasks and put to work, mining when not in use. A mining rig can be an expensive sophisticated computer or it could be a homemade ensemble built with affordable graphics cards. The more powerful a rig is the more hashes it can process per second and the more successful it will be.
Miners can join together to combine resources in a mining pool
How does a mining rig work?
Mining rigs work by using mining software to link the hardware to a pool of miners and pointing its hash rate at the pool and joining in verifying and completing transactions on the network.
Rewards are given when a rig helps the pool of computers add a block to the blockchain.
There are two different different types of mining rig
CPU mining rigs and GPU mining rigs. With the latter being more common now, due to better performance. It can still be worthwhile mining newer alt coins with a CPU rig. But as it is slower it generally a less profitable method.
A GPU mining rig uses a high end graphics card, which has more hashing power than a CPU rig, and can be used to mine different cryptocurrencies with different hashing algorithms.
An efficient GPU rig can be expensive.
What is a Hash?
The first thing to note about a hash is that it is a ‘one way’ function.
A Hash function is an algorithm that can be run on a digital record and it will output a string of numbers and text. This is called a Hash. A digital record can be anything from a video, document or details of a transaction. In fact, any file on a computer. This is because whenever a computer reads or processes any ‘file’ it just sees as a series of 0 and 1. This is called Binary and is the basis of all computer related things.
Each time the same ‘file’ is put through the hash function it will output exactly the same result.
But if the file is changed even in the slightest way, (like adding a comma in a book) then the output would be completely different. Therefore is impossible to process in the opposite direction and find out the original content from the hash.
What is Hash rate?
Hash rate is the number of calculations per second that the hardware can perform every second. Hash rates are measured in megahashes (MH/s), gigahashes (GH/s), and terahashes (TH/s) per second.
A crypto mining rig needs a high hashrate to have more chance of winning the race to secure and verify transactions.
Mining consumes a lot of power and electricity costs are consequently quite high.
So Basically the Hash rate is the number of guesses per second that the mining rig can perform
What is a Merkle Tree?

A Merkle tree is part of a blockchain that is essential to verify the integrity of data.
Blocks in the chain can contain multiple transactions for example if a block contains 4 transactions each transaction is passed through a hash function to produce four hashes.
These four hashes are each combined into pairs and put through the hash function to produce two hashes and these two hashes are again put through the hash function to produce a root hash.
The root hash can be used to verify any of the transactions and this set of hashes is called a Merkle Tree.
There is a Merkle root in every block made-up from the hashes of all its transactions.
Blockchain payments
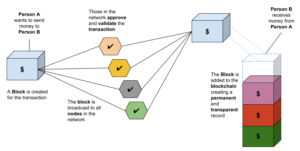
The following diagram shows the simplified process for sending a payment using a blockchain based digital currency, such as Bitcoin. The scenario is that Person A wants to send Person B some money.
In this diagram the concept and function of miners is not shown. Their role would appear within the network approving and validating the transaction. Miners are effectively competing for the chance to approve the transaction and claim the reward. Everyone in the network validates the transaction, then starts work on the next block.
A history of digital currencies.
The concept of digital currencies is not new. Many attempts were made during the technology boom of the 90s using a Trusted Third Party approach but for various reasons such as fraud, financial problems and personal conflicts, these companies failed, and with them the digital currency.
You have no doubt heard of, and probably even used, PayPal. Paypal was launched with ambitions to be a digital currency, but morphed into a digital payments system.
Peter Thiel, co-founder of PayPal:
“PayPal had these goals of creating a new currency. We failed at that, and we just created a new payment system.” [SOURCE]
Why ‘Cryptocurrencies’?
The record keeping consensus process is secured with strong cryptography which masks everything with a complicated code that can only be understood with the public or private keys.
Built on basic cryptography every Cryptocurrency transaction is a file containing the public keys (wallet addresses) of the sender and recipient and the amount of coins transferred. The transaction also needs to be signed with a private key by the sender. In a cryptocurrency network ‘miners’ solve a cryptographic puzzle to confirm transactions by using their own computer processing power. The miner receives a reward, plus a transaction fee in return. The transaction needs marked as legitimate before it is broadcast to the network. When a transaction is confirmed every node in the network adds it to its database and it becomes permanent, irreversible and unforgeable.
Cryptocurrency networks are based on absolute consensus that balances and transactions made are completely legitimate. If nodes on the network were to disagree on any balance, the system would not function. There are pre-built rules programmed into the network to prevent this type of crash occurring.
Other uses of blockchain technology
Blockchain apps don’t have to be just payments systems or cryptocurrencies. It could be anything, like a social network, a learning platform anything where you are looking to remove the ‘trusted’ third party.
Blockchain can be used to decentralise other things besides banking, as we migrate more and more data to the ‘cloud’ prevalent blockchain offers additional security and less reliance on vulnerable centralised companies who ultimately control the security of, and cost of, storage.
Peer to peer messaging, social networking, and websites, can leverage blockchain encryption for security, resilience to censorship, and even to provide dynamic customized content to visitors.
Verifiable and auditable voting systems could use blockchain technology to ensure voting is tamperproof and legitimate. Blockchain can be applied to pretty much any situation requiring proof of ownership from property to works of art as advanced protection against theft.
